Canary Receives IoT Security Certification From ICSA Labs
At Canary, we want to redefine your expectations with new hardware, new features and new services that improve your experience. Most of these additions are immediately apparent, such as the recently launched Canary Flex, and our Membership rollout. However some of the effort we put into Canary happens behind the scenes, although it’s just as important. Data security is one of them.
As Internet-connected devices become increasingly prominent in our homes, securing them from misuse becomes increasingly important. Smart light bulbs, thermostats, washers and dryers, refrigerators, hairdryers and, yes, home security cameras could be—and have been—exploited if security isn’t taken seriously. It goes beyond encryption, which is why we worked with independent security firms to put Canary through the most rigorous security testing available.
We go to great lengths to ensure Canary is as secure as possible. That’s why we’re proud to be the first device to receive IoT Security Certification from ICSA Labs.
A Security First For IoT Devices
Testing for IoT security is in the early stages, much like the industry itself. Independent certification ensures a standard that must be met by a product. For consumers, seeing the UL certification on a product means it has been tested for safety.
“In an industry as fast growing and diverse as the Internet of Things, security is too often an afterthought,” said Chris Rill, co-founder and CTO of Canary. “Until now, there hasn’t been a trusted resource to vet many of the connected home products currently flooding the market.”
ICSA Labs, an independent branch of Verizon, is the first entity working to create an IoT security standard. With more than 25 years of experience testing and certifying security products, it makes sense ICSA Labs would want to ensure the security of IoT devices through a rigorous testing process.
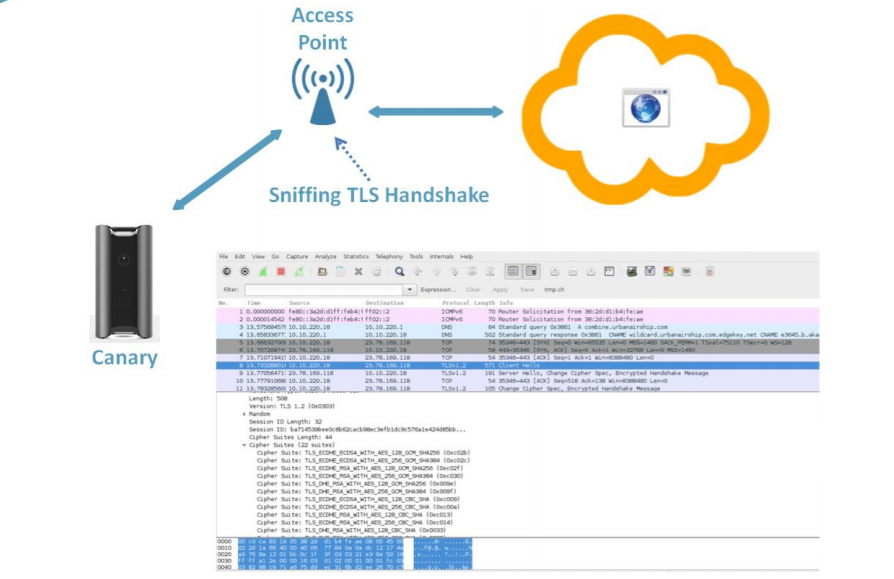
As part of the IoT security certification process, ICSA Labs tested three areas of Canary for any vulnerabilities —communications sent and received, user interface and the device itself. In order to ensure Canary was secure, the lab even acted as a malicious actor and tried to trick Canary into accepting the connection.
“Canary is the first product to attain ICSA Labs Internet of Things (IoT) Security Certification after successfully meeting all of the requirements against which it was tested,” the lab concluded in its report.
The Canary Defense
As noted by ICSA Labs, a key feature of Canary is the lack of attack surface—the number of attack points of hardware or software. The only way to access Canary is through the user’s app, which greatly reduces the number of potential holes a hacker could exploit.
“We worked from day one to make sure Canary can sit securely in your home,” said Rill.
Much like you want your bank to have the best encryption possible to keep your information safe, the same is true for any communication between your device and the cloud. ICSA Labs verified that all Canary communication is secure.
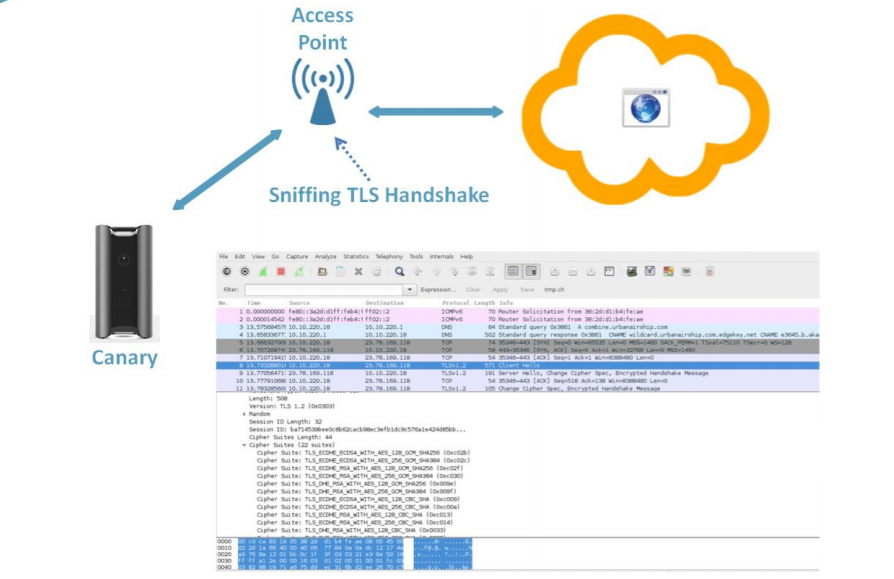
“The only entities the Canary really communicates with are servers in the Canary cloud and it does so almost always over an encrypted channel. Of the rare occasions when communications are not encrypted, no sensitive information is transmitted,” reads the ICSA Labs report.
ICSA tested the Canary app along with Canary. The iOS and Android apps follow best security practices to protect any local data stored on your phone can’t be exposed by other applications on your device. Any communication between the app and the Canary cloud is encrypted. Even with ICSA performing man-in-the-middle attacks or using modified security certificates, the Canary app was not fooled.
IoT Security And You
Beyond your personal data, IoT vulnerabilities can be exploited in hacking campaigns. Most recently, an attack using an army—dubbed the Mirai botnet—of hacked network-connected cameras, DVRs and other IoT devices on Dyn, a major DNS host, was behind the worldwide outages of Twitter, Spotify, PayPal, the New York Times and many other sites on Oct. 21.
The IoT devices used in the attacks had extremely weak security that hackers were able to exploit with a default password. Because many devices are listening for inbound commands, hackers can send a request for access by providing fake credentials. In the case of the Mirai botnet, hackers used easily found default passwords to take over thousands of devices to send junk data to knock websites offline.
Canary devices were not used in these attacks. In addition to the encryption measures listed above, Canary has no way to listen for inbound requests. A hacker can’t request access to Canary to take it over.
Even with this IoT Security Certification, Canary’s mission to constantly improve is not over. We will continue to work hard to follow industry best practices and explore new ways to pursue and promote security.

2 thoughts on “Canary Receives IoT Security Certification From ICSA Labs”
You must be logged in to post a comment.